
Where are most of the US Military’s secrets and not so secrets ending up? Not in one of the cybercriminal hotbed countries, but in the ancient trading post on the trans-Saharan caravan route, the city of Timbuktu. For some, it may seem odd that this would be where many US Military secrets were ending up. For IT folks specializing in email (after reading below) it will all make sense…
Let’s dig in to find out why and how ***and we’ll even provide this tip that we hope you will share with your US Military friends and all of those who may be contractors or communicating with military folks as a way to stop this information leak. (P.S. we believe this type of issue is more widespread than the within and around the US Military).
Email is sent instantly to the email address designated. Once it hits the Internet, there is no way to “recall it”. And, the reality for the US Military is that many thousands of email every month route due to human error to Timbuktu. Why is Timbuktu the largest repository of US military email (and importantly email from contractors and suppliers communicating with military folks by email)? The domain extension for Mali (where Timbuktu is), is .ml. By contrast, the domain extension for the US Military is .mil.
According to the Financial Times, in the last several months alone, more than 100,000 emails that senders thought were heading to US Military colleagues – for example email that was thought to be sent to General@Army.mil were actually sent to General@Army.ml. Rather than email heading across K Street in Washington, D.C., it takes a turn and routes to Mali (the owner of the .ml domain suffix) and winds up in the hands of the Mali military stationed in Timbuktu!
Since instead of appending the military’s .MIL domain to a recipient’s email address, people frequently type .ML, the country identifier for Mali, by mistake, we’ll chalk this up to human error rather than espionage.
According to a report in the Financial Times, many of the emails include medical records, identity document information, lists of staff at military bases, photos of military bases, naval inspection reports, ship crew lists, tax records, and more. Some of the misdirected emails were sent by military staff members, travel agents working with the US military, US intelligence, private contractors, and others.
Now, you might think these emails should “bounce back” but they don’t, as the “bounce back” feature is entirely dependent on the recipient email server settings. And the recipient server is set to receive these.
Of course, we at Tech Essentials have a simple solution.
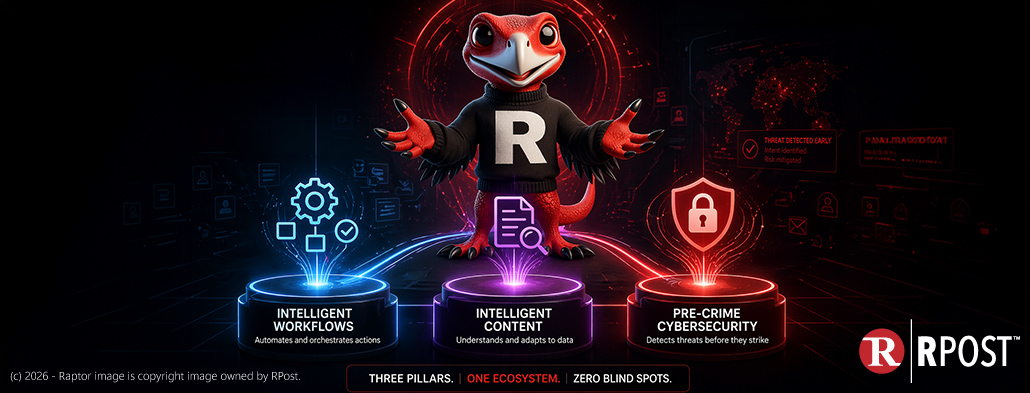
RMail’s “Right Recipient” feature can be configured to detect and alert the sender after they click send but before the message leaves their Microsoft Outlook interface if the email looks like it might be going to a destination that was not intended. And, for even more protection, with RDocs™ document security, if you discover later you have mis-sent a sensitive document anywhere, you can kill that document out in the ether, even if it is in someone’s inbox in Timbuktu. And even better, you can with confidence see if anyone accessed that data BEFORE you realized and killed it.
Know More: Document Control
This means, if you mis-send some military secrets to Timbuktu during the daytime in Washington, DC, you can “kill it” in Timbuktu in the middle of their night, and retain proof the message and documents were killed before any viewing of it.
And, for those who send sensitive civilian documents (lawyers, insurance professionals, investment advisors, health care professionals, and others), you should think about how these two add-ins to your email and document sending can perhaps save the day for YOU, if you were to be susceptible to the “mis-send” of a sensitive email.
Contact RPost for more information on these sensitive email sending features.

May 22, 2026

May 15, 2026

May 08, 2026

May 01, 2026
April 24, 2026