
On Sunday, more than a hundred media outlets around the world, coordinated by the Washington, DC-based International Consortium of Investigative Journalists (“ICIJ”), released stories on the “Panama Papers”, which is an exposé of private client and internal work product emails and other files. More than 5 million emails and files were stolen from within the IT systems of the exclusive Panamanian law firm Mossack Fonseca. World leaders and U.S. business people have become targets as a result of the exposed data.
There is no doubt, from reading the whirlwind of press on the “Panama Papers”, that the majority of this correspondence would not have been admissible in civil court actions due to being protected as attorney-client privilege or attorney work product privilege. It is also likely that the person who provided the trove of data to the press violated a corporate non-disclosure agreement or committed an Internet crime.
But for legal practitioners, in today’s environment of massive and immediate dissemination and worldwide (Internet) publication of exposed confidential information, does that really matter? If one can point to public release of the information, does that circumvent attorney-client and work product privilege? One might argue (and we will likely see these arguments more often) that in the new era of published leaks, attorney-client privilege is becoming obsolete — at least if all the correspondents do is add an “old fashioned” signature line to one’s email, or a subject line phrase that makes the statement that the plain text email correspondence (think written and mailed electronic postcard) has information so sensitive that the parties intended the information to remain private and protected.
With the “Panama Papers”, an anonymous “whistleblower” was able to secretly send journalists the massive set of emails and files which were then circulated to more than 400 reporters in secret over more than a year, before a coordinated effort to go public, according to ICIJ. The whistleblower and the ICIJ that coordinated the effort took great care to use encryption to mask their correspondence, according to Wired Magazine. It is unfortunate for the Mossack Fonseca law firm clients that neither the firm nor the clients appear to have been so careful.
Who might the whistleblower have been?
Perhaps this was a hacker that gained access to the firm’s IT systems. Or, perhaps this was a disgruntled IT staffer, consultant, or outsourcer that copied the database of files before leaving the firm, and then sold it to some third party. How much did they sell it for? $10,000? $100,000? $1 million? Whatever the price, the reputational damage to Panamanian law firm Mossack Fonseca and its clients is far greater.
In these scenarios, it is important to remember that plain text email correspondence can be exposed in route in many ways, and certainly on a company’s mail servers, anyone with access can read these messages at will.
Let’s assume IT staffs are loyal and committed to using best efforts to protect their employees and employers, and as such, they often go the extra step of setting up encryption at the mail gateway – – so everything leaving the firm is encrypted when it hits the Internet. We know, however, that they often cannot control what happens to your message upon receipt at the recipient destination, and often it is out of their control if email archives store messages and attached files unencrypted and are somehow accessed by an unauthorized person. The “whistleblower” treasure trove, as we may find out from Mossack Fonseca, may have been the email archive (in house or outsourced) database containing the unencrypted messages before sent at the mail server (before reaching the Internet) and after received (from senders by the mail server and perhaps decrypted by the mail server).
Whatever the source, the important learning is to consider what might one do when one needs to communicate with one’s client or among staff with sensitive client matters? We suggest trust no one, and use “Outbox-to-Inbox” email encryption rather than “network-level” or “policy-based gateway” encryption, if your information is sensitive to the highest degree.
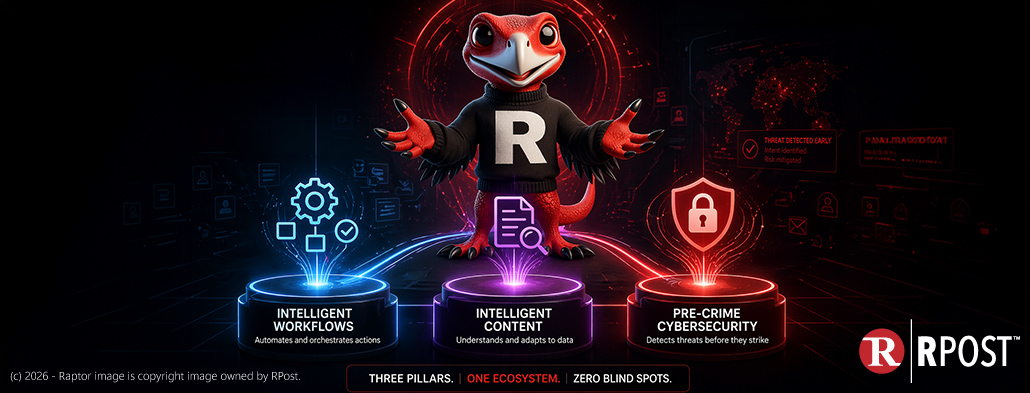
RMail encryption calls this “Outbox-to-Inbox” email encryption “Executive Mode” encryption and recommends use for those dealing in merger, acquisition, corporate litigation strategy, private client wealth management, and personal health matters; matters that one would like to shield from their IT staff or the IT staff at the recipient.
RMail® Executive Mode encryption encrypts the message locally in the sender’s Microsoft Outlook program at the sender’s desktop or device, and ensures encrypted delivery straight through to the recipient’s desktop; securing from the potential of data breaches both within the sender’s in-house or outsourced email system, and external while in transport across the Internet and within the recipient’s email system. This also provides for letting the recipient encrypt replies without having RMail at their end.
With RMail® Executive Mode encryption, the message and all attachments remain encrypted within the recipient’s email inbox, and are printed and encapsulated inside a PDF file, readable after decrypting in one’s PDF reader (outside of the inbox) and if saved, remain saved in encrypted file format unless the recipient extracts the attachments and chooses to use them as normal files. This end-to-end encryption uses a 256-bit AES encrypted PDF wrapper to keep one’s message and any attachments private from start (while sitting in outbox) to finish (even while sitting within their inbox), so only one’s recipient can read them.
There are other ways to do something similar, using PKI or PGP encryption, but in each of these methods, depending on how deployed, the message is decrypted in the recipient’s inbox and remains so, are usually too complicated for normal senders and normal recipients to use, or requires special software at the recipient end which introduces more complexity.
Would RMail® Executive Mode encryption have protected Mossack Fonseca clients from this mega leak? It may have. It certainly should have at least been an option in the client or lawyer toolkit to protect information in this new era of mega leaks.

May 15, 2026

May 08, 2026

May 01, 2026
April 24, 2026

April 17, 2026