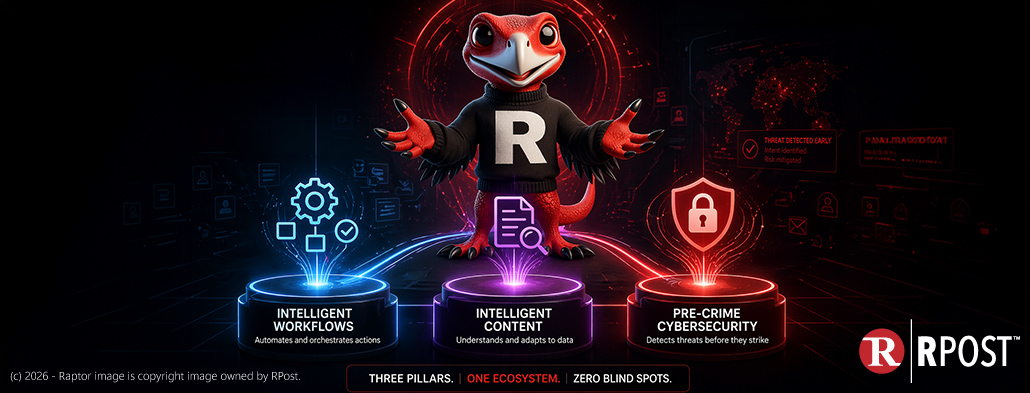
Rocky the Raptor here, your sharp-clawed cybersecurity evangelist, here to rip apart some old myths about Man-in-the-Middle (MITM) attacks - those sneaky tactics most people think they understand, but few realize just how far they’ve evolved.
For decades, the big consultancies (think Accenture with a market cap down $60 Billion in recent days, McKinsey, and their luxury-suit-wearing cousins) were the ticket to big-picture guidance.
Rocky the raptor here, RPost’s cybersecurity product evangelist. I thought we’d have some cybersecurity fun today and play a little game of “This or That”. Meaning, I will present two options, and you pick which you prefer, this one or that one.
Rocky the raptor here, RPost’s cybersecurity product evangelist. I’ve seen a lot from my perch high above the cyber battlefield. Here’s a fact: once a cybercriminal makes their move, they’re not lumbering around looking for an open door; they’re sprinting through it, dumping your data into the dark web before you’ve even had your first coffee.
Rocky the raptor here, RPost’s cybersecurity product evangelist. I must say, cybercriminals are quite opportunistic. They seem to prey on current trends and seasonal timing. For anyone with kids (loosely defined, folks up to their mid-20’s), you ought to share this article --- before it is too late for them.

May 01, 2026
April 24, 2026

April 17, 2026

April 10, 2026

April 03, 2026